Data Is the New Oil… or Is It?
At Skeddly we’re focused on bringing you the best in AWS help tutorials, AWS scheduler services, and AWS backup services. However, from time to time we like to reach out to other leaders in the AWS space to help you, our blog readers, stay on top of the latest developments and news within the AWS ecosystem.
Today Skeddly had the opportunity to speak with Remy Rosenbaum, VP, Marketing & Analytics at Caserta, a big data and analytics company that helps businesses harness the power data to exceed their business goals.
Without further ado, let’s jump into the interview.
Comparing Managed MySQL Services on AWS, Azure, and GCP
MySQL is a popular open-sourced relational database server. It comes in many flavours, including Enterprise and Community editions.
Amazon Web Services, Microsoft Azure, and Google Cloud Platform all provide their own managed MySQL services. The available versions and features vary from provider to provider. As an added complexity, AWS provides three different MySQL services, each one of them different. Let’s take a closer look.
Switching to the Cloud: Any Change Is Going to Be Challenging, Even If It's for the Better
At Skeddly we’re focused on bringing you the best in AWS help tutorials, AWS scheduler services, and AWS backup services. However, from time to time we like to reach out to other leaders in the AWS space to help you, our blog readers, stay on top of the latest developments and news within the AWS ecosystem.
Today Skeddly had the opportunity to speak with a few of the bright minds behind Keyhole Software, a cutting edge technology company with an impressive amount of AWS experience. Below, we talk about the approach they used to build their dev studio from a 2 person show serving only one client to a 100 person team serving over 25 enterprise clients.
Without further ado, let’s jump into the interview.
Enable EBS Fast Snapshot Restores Action
A month ago, Skeddly added a Disable EBS Fast Snapshot Restores action. This action is a fantastic way to ensure you don’t leave EBS snapshots around with Fast Snapshot Restores enabled. That will just be a waste of money.
Today, I’m happy to announce a new Skeddly action: Enable EBS Fast Snapshot Restores. This new action allows you to enable, and optionally disable Fast Snapshot Restores on your EBS snapshots.
Comparing Managed Redis Services on AWS, Azure, and GCP
Redis is an in-memory data store. It’s predominantly a key/value store, so it does not have features in many relational databases. It can be used as a simple database, a cache, or as a pub/sub system. Since it’s all in-memory, it is very fast, but it also requires alot of memory.
Amazon Web Services, Microsoft Azure, and Google Cloud Platform all provide their own managed Redis services. The available versions and features vary from provider to provider. Let’s take a closer look.
With Such a Flurry of New AWS Offers, It's Easy to Get Overwhelmed and Miss What's Useful for eCommerce
At Skeddly we’re focused on bringing you the best in AWS help tutorials, AWS scheduler services, and AWS backup services. However, from time to time we like to reach out to other leaders in the AWS space to help you, our blog readers, stay on top of the latest developments and news within the AWS ecosystem.
Today Skeddly had the opportunity to speak with Denis Zlatov, the Co-founder and Customer Success Officer at JetRails, a mission-critical website hosting provider that is best known for providing premium hosting for eCommerce websites. JetRails also use AWS as one of their main tools of choice when working on client projects.
Without further ado, let’s jump into the interview.
Disable EBS Fast Snapshot Restores Action
A few weeks ago, Amazon announced a new feature for EBS snapshots: Amazon EBS Fast Snapshot Restore (FSR). Normally, accessing data on new EBS volumes was quite slow as the data is lazy-loaded from S3. When Fast Snapshot Restore (FSR) has been enabled on an EBS snapshot, new EBS volumes created from that snapshot will allow fast data access.
While this feature is very good, it’s very expensive to keep enabled on an EBS snapshot for a long time. The cost is $0.75 per EBS snapshot, per availability zone enabled, per hour. From the blog post:
You pay $0.75 for each hour that Fast Snapshot Restore is enabled for a snapshot in a particular Availability Zone, pro-rated and with a minimum of one hour.
During a 30-day month, the cost would be a whopping $540 per EBS snapshot, per availability zone enabled.
Today, I’m happy to announce a new Skeddly action: Disable EBS Fast Snapshot Restores. This new action allows you to disable the fast snapshot restores on one or more EBS snapshots, stopping the extra hourly charge.
Introducing Managed Backups
Today, I’m happy to announce a significant new feature to Skeddly: Managed Backups.
Using Managed Backups, you:
- Create a backup plan that defines your backup schedule and retention policy,
- Add resources to your plan,
- Sit back and relax.
Once you have created your plan and added resources, Skeddly will create the necessary actions to create and delete those backups according to your desired schedules.
Introducing Projects
Today, I want to tell you about a new feature just added to Skeddly: Projects.
Skeddly “Projects” are a way to segregate and organize your credentials and actions. Each project is an isolated collection of cloud credentials, actions, and Managed Instances. You can think of a project as an account within an account.
If you are an MSP managing resources for multiple clients, Projects can help you.
If you manage multiple environments that you want to keep separated, Projects can help you.
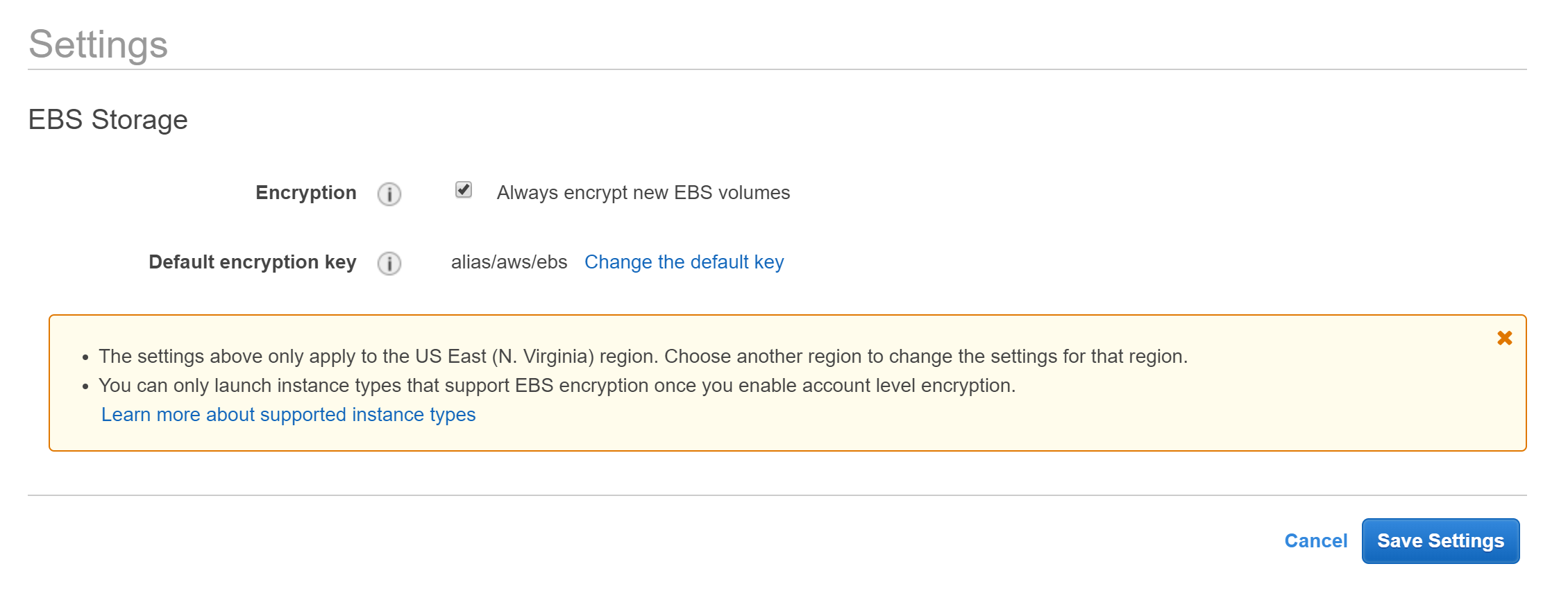
Use Caution When Enabling Default Encryption of New EBS Volumes
Amazon has enabled a great new feature for cloud security: Default Encryption for New EBS Volumes. When enabled in a region, any new EBS volume that is created will automatically by encrypted with the configured KMS key.
At first glance, this sounds great. However, here there be monsters, as the saying goes, if you are copying EBS snapshots or AMI images across AWS accounts.