Use Caution When Enabling Default Encryption of New EBS Volumes
Amazon has enabled a great new feature for cloud security: Default Encryption for New EBS Volumes. When enabled in a region, any new EBS volume that is created will automatically by encrypted with the configured KMS key.
At first glance, this sounds great. However, here there be monsters, as the saying goes, if you are copying EBS snapshots or AMI images across AWS accounts.
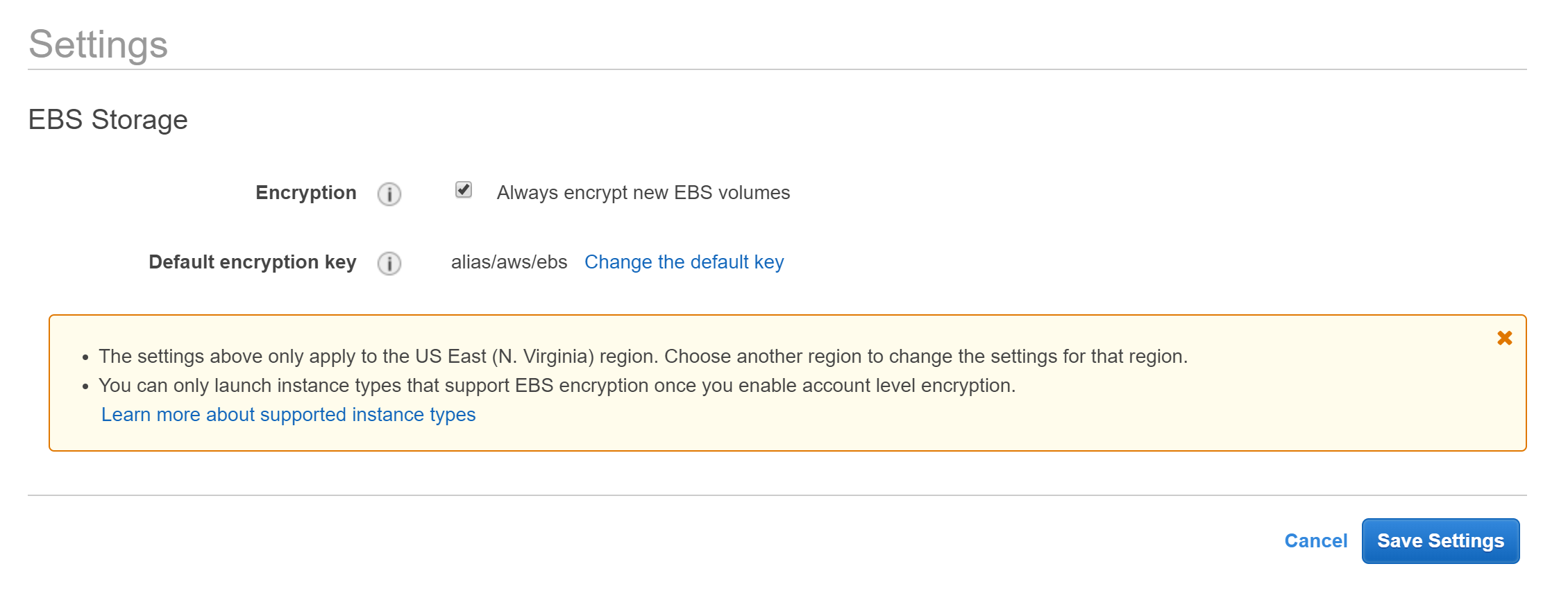
Your first instinct may be to enable Default Encryption using the default KMS key aws/ebs. However, by doing this, you won’t be able to share any EBS snapshots or AMI images, or copy them to another AWS account.
EBS snapshots and AMI images that are encrypted using aws/ebs cannot be make public nor shared with other AWS accounts. And without sharing, they cannot be copied.
According to Sharing an AMI with Specific AWS Accounts:
If you share an AMI with encrypted volumes, you must also share any CMKs used to encrypt them.
And you cannot share the default aws/ebs KMS key.
According to Sharing an Amazon EBS Snapshot:
When you share an encrypted snapshot, you must also share the customer managed CMK used to encrypt the snapshot. […] AWS prevents you from sharing snapshots that were encrypted with your default CMK. Snapshots that you intend to share must instead be encrypted with a customer managed CMK.
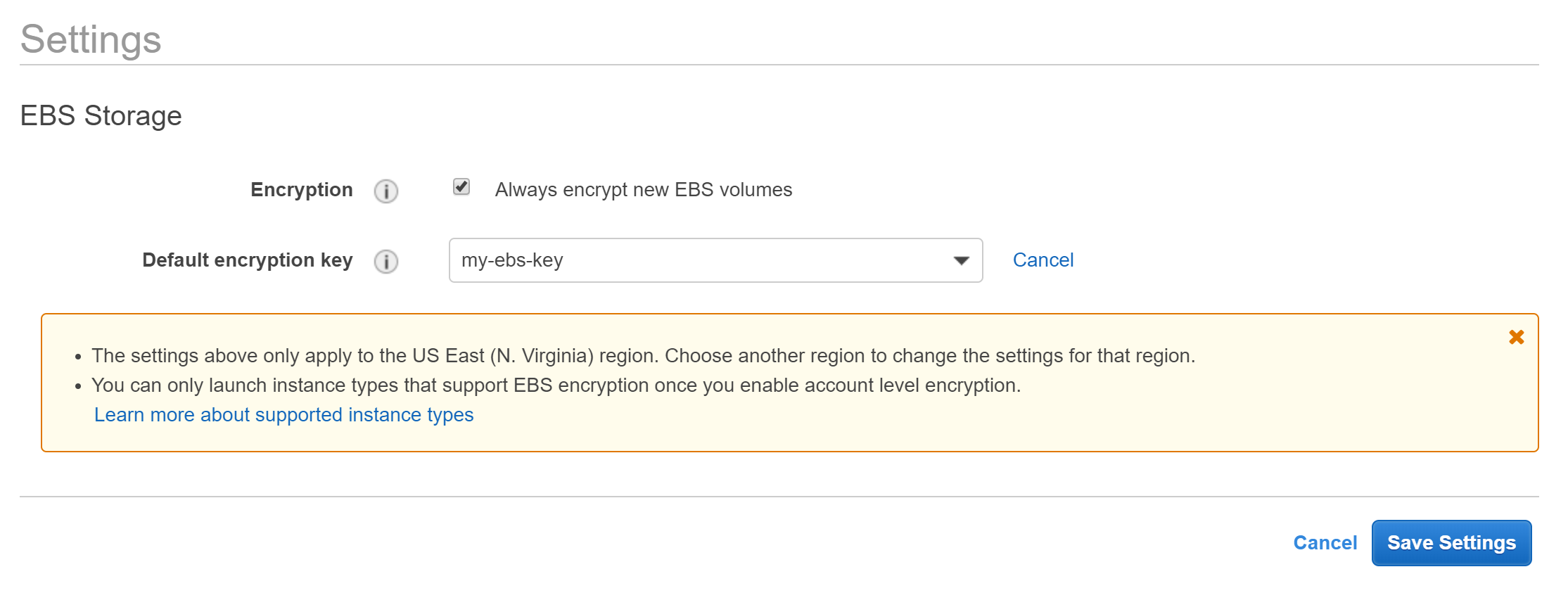
So, if you are even hinting at the thought of copying your backups to another AWS account, be pro-active and create your own KMS key and use it for Default Encryption of EBS volumes.
Also note, that if you currently have an automatic process of copying EBS snapshots or AMI images across accounts (either using a 3rd party or you created it yourself), enabling Default Encryption using aws/ebs will break that once you’ve created new EBS volumes and snapshots.
About Skeddly
Skeddly is a kick-ass managed scheduling service for your AWS account. Sign-up for our 30 day free trial or sign-in to your Skeddly account to get started.