Encrypting an Unencrypted RDS Snapshot
RDS snapshots can be unencrypted or they can be encrypted at rest. Today, best practice is to use encryption-at-rest on your RDS instances and clusters, and to encrypt your RDS snapshots.
When you create an RDS snapshot from an RDS instance or cluster, the resulting snapshot will be encrypted if the source instance or cluster is encrypted. But if the source is not encrypted, then your RDS snapshot is not encrypted. When you create an RDS snapshot, you are not given the option to encrypt it.
However, when you copy an RDS snapshot, you can add or change the KMS keys used. So, if you have an unencrypted RDS snapshot that you want to encrypt, you can encrypt it by copying it, encrypting it along the way.
Using the AWS Management Console
To encrypt an unencrypted RDS snapshot using the AWS Management Console, you can follow these steps:
Step 1: Find the snapshot that you want to encrypt, and select it by clicking the checkbox next to it’s name. You can select a “manual” snapshot, or one of the “automatic” snapshots that are prefixed by “rds:”.
Step 2: From the “Snapshot Actions” menu, select “Copy Snapshot”.
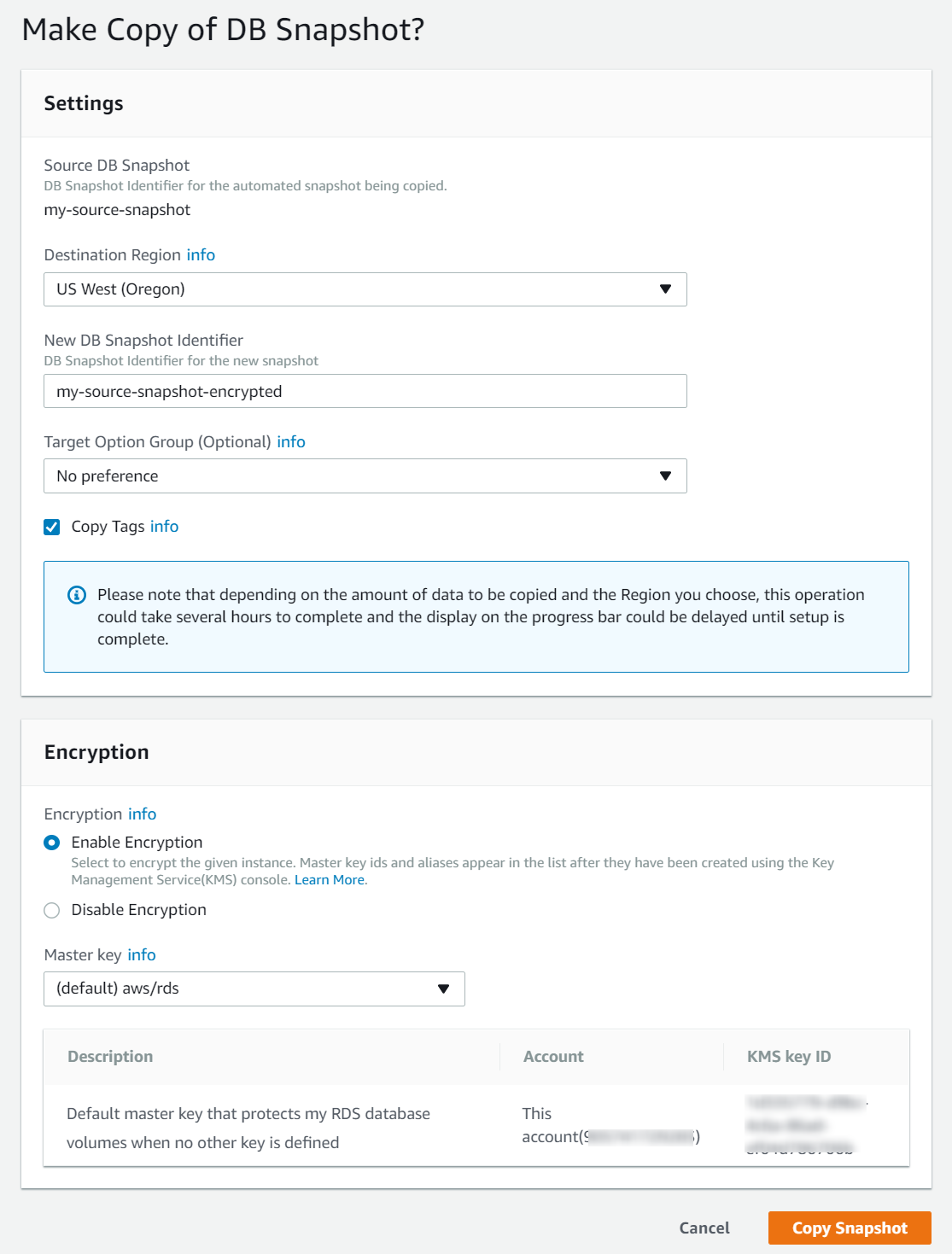
Step 3: On the page that appears:
- Select the target region. In this case, we’re selecting the same region as the source snapshot.
- Specify your new snapshot name in the “New Snapshot Identifier” field. This identifier must not already be used by a snapshot in the same region.
- Check the “Copy Tags” checkbox if you want the tags on the source snapshot to be copied to the new snapshot.
- Under “Encryption”, select the KMS key that you want to use to encrypt your snapshot.
- Click the “Copy Snapshot” button.
Step 4: Wait for the snapshot to complete.
Once the copy is initiated, you should return to the RDS snapshots page. Your new snapshot should appear in the list with a status of “creating”. The snapshot’s status will become “available” once the copy process is complete.
AWS CLI and SDKs
If you want to encrypt your RDS snapshot using the AWS CLI, it can be done using the following command:
aws rds copy-db-snapshot \
--source-db-snapshot-identifier my-source-snapshot \
--target-db-snapshot-identifier target-snapshot \
--kms-key-id <kms key>
The KMS key used in this command can be either:
- The KMS key ID (
00000000-0000-0000-0000-000000000000), - The KMS key ARN (
arn:aws:arn:us-east-1:123456789012:key/...), or - A KMS key alias (
alias/my-alias)
If your RDS snapshot is an Aurora cluster snapshot, then use copy-db-cluster-snapshot instead of copy-db-snapshot in the command above.
About Skeddly
Start automating your RDS backups today by signing up for our 30 day free trial or sign-in to your Skeddly account to get started.